May 14, 2026
Assistant Director of Chapters
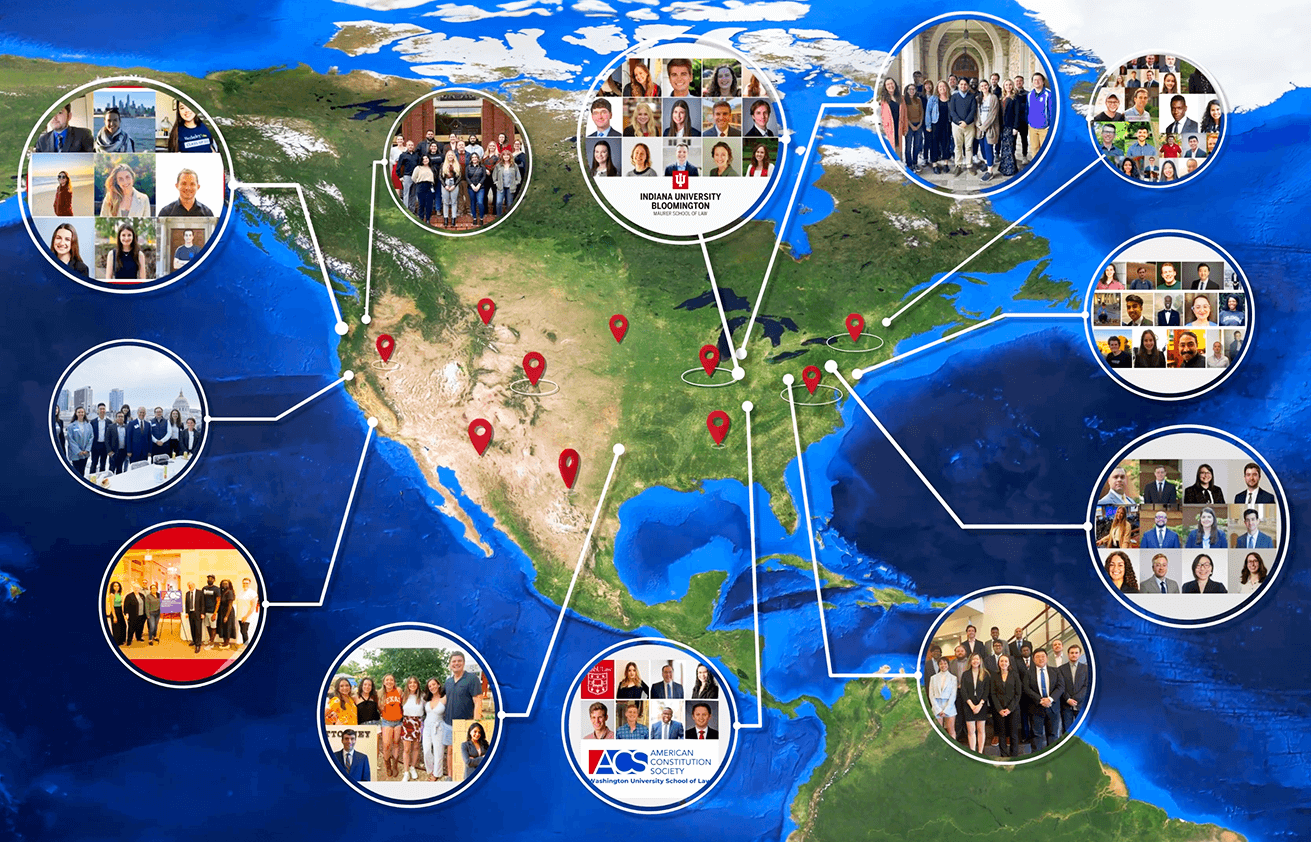
The American Constitution Society for Law and Policy (ACS) is the nation’s foremost progressive legal organization, with a diverse nationwide network that includes nearly 250 student and lawyer chapters, and progressive lawyers, students, judges, scholars, elected officials, and advocates. Our mission is to support and advocate for laws and legal systems that redress the founding failures of our Constitution, strengthen our democratic legitimacy, uphold the rule of law, and realize the promise of equality for all.
ACS has an immediate opening for an Assistant or Associate Director of Chapters to manage ACS’s growing network and support the overall work of the Department of Network Advancement. ACS chapters are not only the lifeblood of ACS, but a tailor-made infrastructure for sharing ideas, testing theories, and gathering diverse inputs. Together, and with your support, we will move ACS forward to meet this critical inflection point in our nation’s history. We will continue to build a community around a shared identity and values. We will defend democracy and support those who champion the rule of law. And we will transform our system of law and government into a force for good in all our lives.
RESPONSIBILITIES
The Assistant or Associate Director of Chapters will assist in:
- Strengthening and ensuring the success of ACS’s most valuable asset: its nationwide progressive network. This includes managing and supporting the existing network of ACS student and lawyer chapters across the country, the strategic expansion of new ACS chapters; supporting and facilitating individual chapter programming; and coordinating national programming for ACS-wide leaders.
- Building a vibrant, diverse, active, and cohesive network for members at all stages of their careers;
- Implementing the division’s budget and strategic priorities;
- Integrating chapter activities and chapter members into ACS’s various substantive initiatives;
- Developing and planning signature events to raise money, raise ACS’s profile, and broaden our impact in key legal markets around the country;
- Facilitating outreach to chapter members and outside organizations;
- Empowering, supporting, and uplifting ACS student and lawyer chapter leaders;
- Working to ensure career-long engagement with the ACS network;
- Coordinating the participation of network members with ACS special projects and career opportunities; and
- Other duties as may be assigned from time to time within the department overall.
DESIRED QUALIFICATIONS
The ideal candidate will possess many of the following qualifications and personal attributes:
- Campaign, organizing, or event planning experience;
- Strong attention to detail;
- Ability to absorb and act on dynamic information;
- Ability to exercise sound judgment when navigating collaborations with individuals across the legal profession, throughout the country, across subject matters, and across experience levels (from law students to new lawyers, seasoned lawyers, scholars, judges, and public officials);
- Excellent writing skills;
- Thrives in a collaborative and outcome-driven work culture;
- Performs well in a team environment, but can also consistently accomplish tasks independently;
- Knowledge of current legal and public policy issues;
- Some travel for meetings and events is required;
- JD preferred; and
- Social media and Excel experience are a plus.
The ideal candidate could be based in Pacific Northwest or Southeast with the expectation of occasional travel to Washington D.C., when necessary.
COMPENSATION AND BENEFITS:
- The salary for this position is $50,000-70,000 based on education level and experience;
- 4-day work week schedule;
- Generous health, vision, dental, and life insurance;
- Paid holiday, vacation, and sick leave; and
- A robust and collaborative work environment.
ACS values a diverse workforce and an inclusive culture. ACS encourages applications from all qualified individuals without regard to race, color, religion, gender, sexual orientation, gender identity or expression, age, national origin, marital status, citizenship, disability, and veteran status.
Interested applicants should email a cover letter, resume, & list of three references to jobs@acslaw.org.



